Invite to Our blog, a space where interest fulfills info, and where daily subjects become interesting conversations. Whether you're looking for understandings on way of life, technology, or a little everything in between, you have actually landed in the best area. Join us on this exploration as we study the worlds of the ordinary and phenomenal, making sense of the globe one article each time. Your journey into the remarkable and varied landscape of our Zero Trust Policy Example begins right here. Explore the fascinating web content that awaits in our Zero Trust Policy Example, where we unwind the details of different subjects.
Zero Trust Policy Example

Zero Trust Policy Example
Research HQ The Most Important Principles Of Zero Trust Security
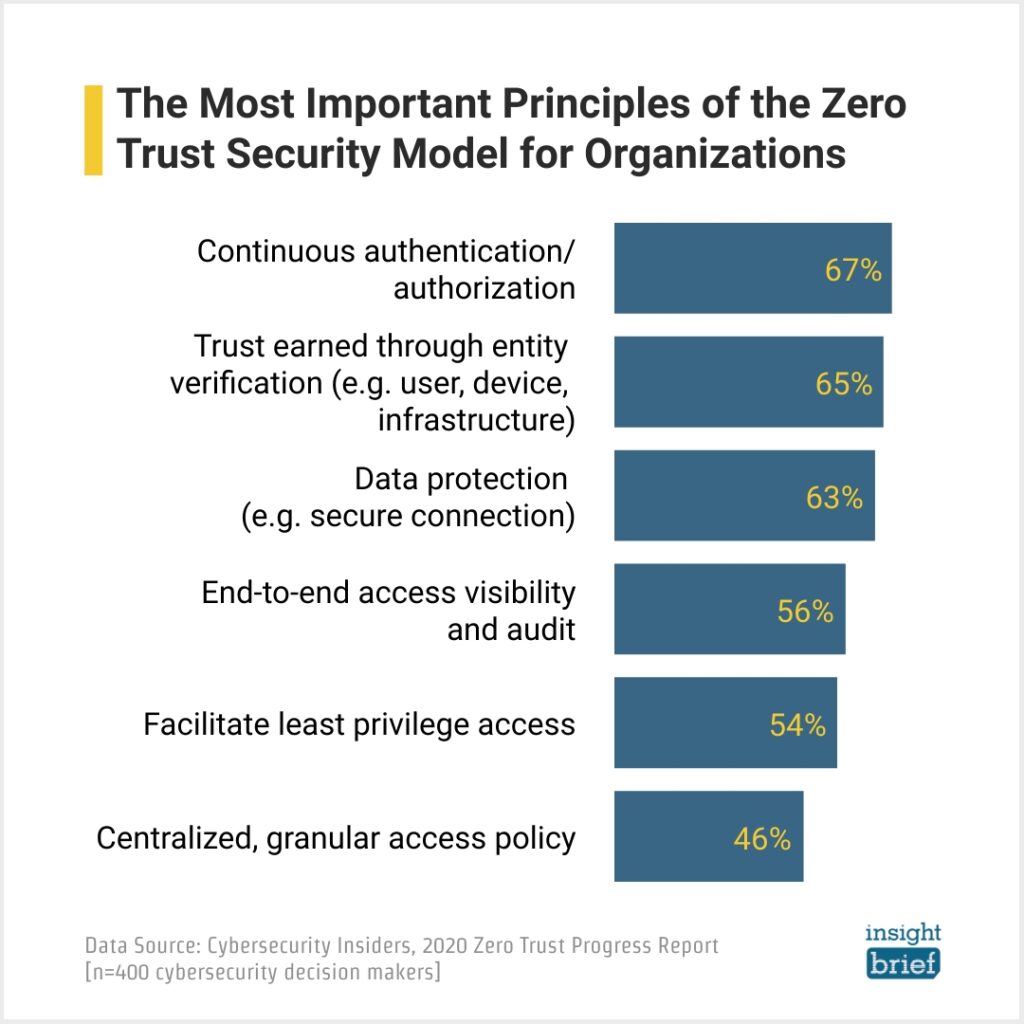
Research HQ The Most Important Principles Of Zero Trust Security
Why You Need Zero Trust Security And How To Implement It

Why You Need Zero Trust Security And How To Implement It
Gallery Image for Zero Trust Policy Example
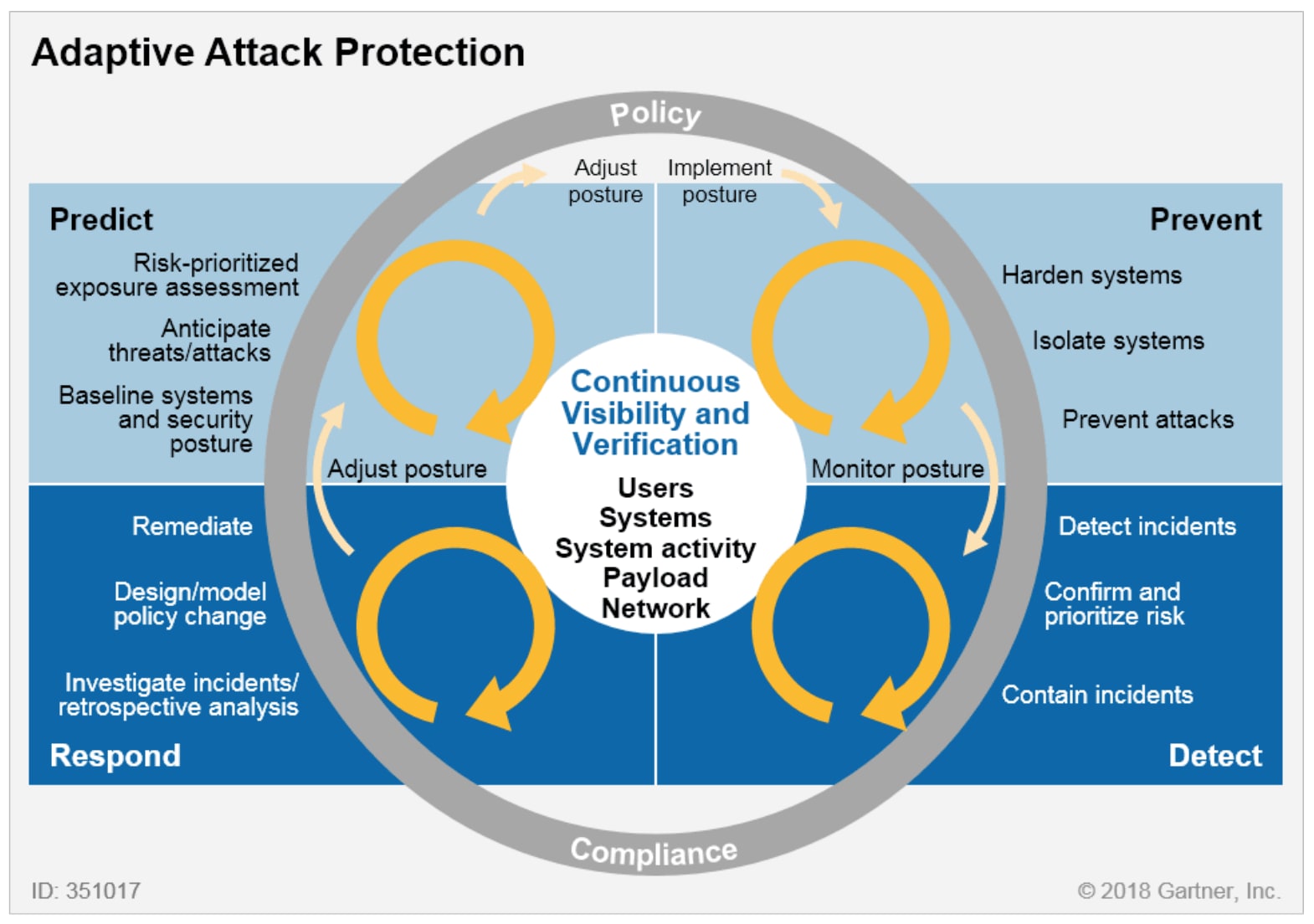
The Gartner CARTA Model

What Is Zero Trust Security CoreView
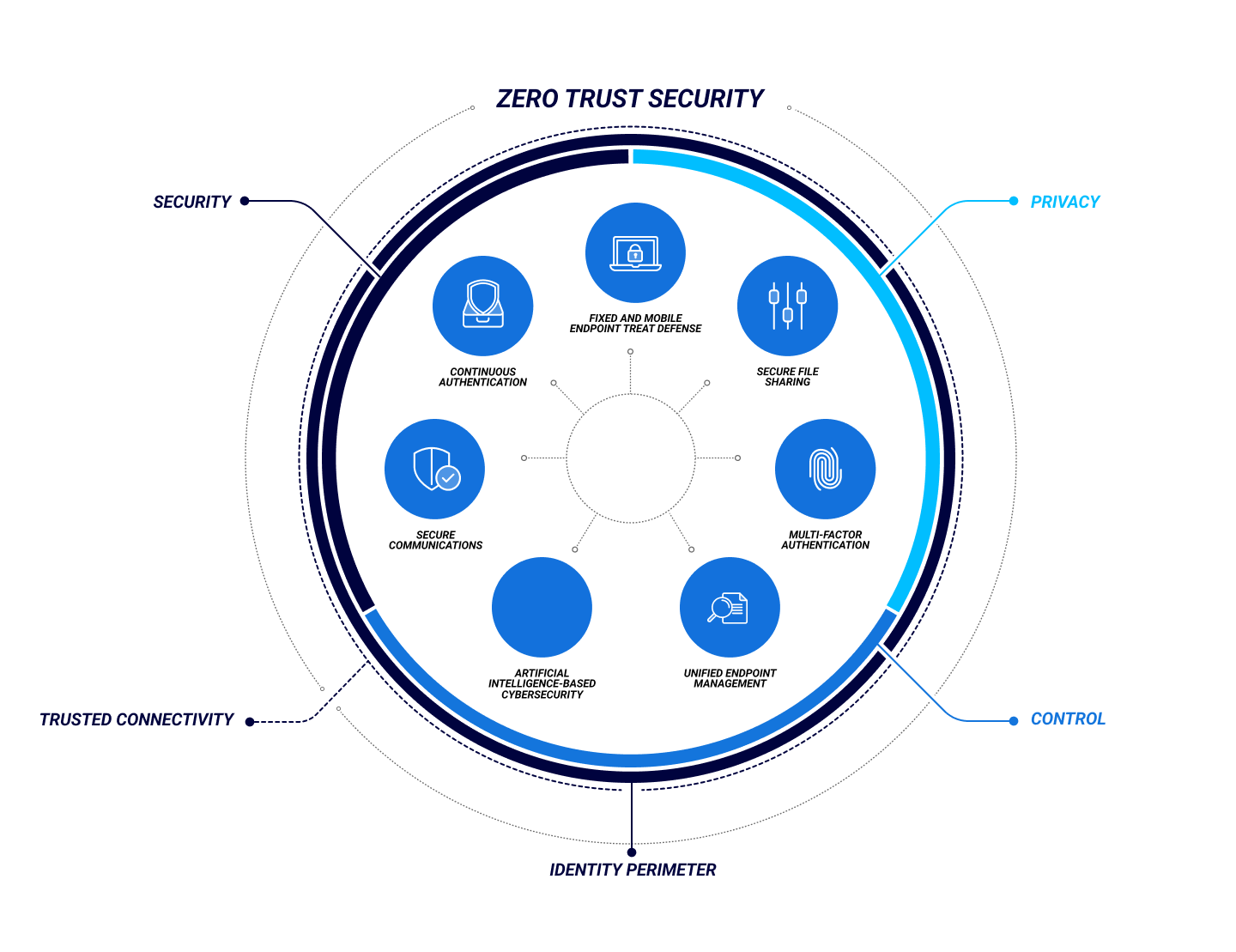
What Is Zero Trust Security
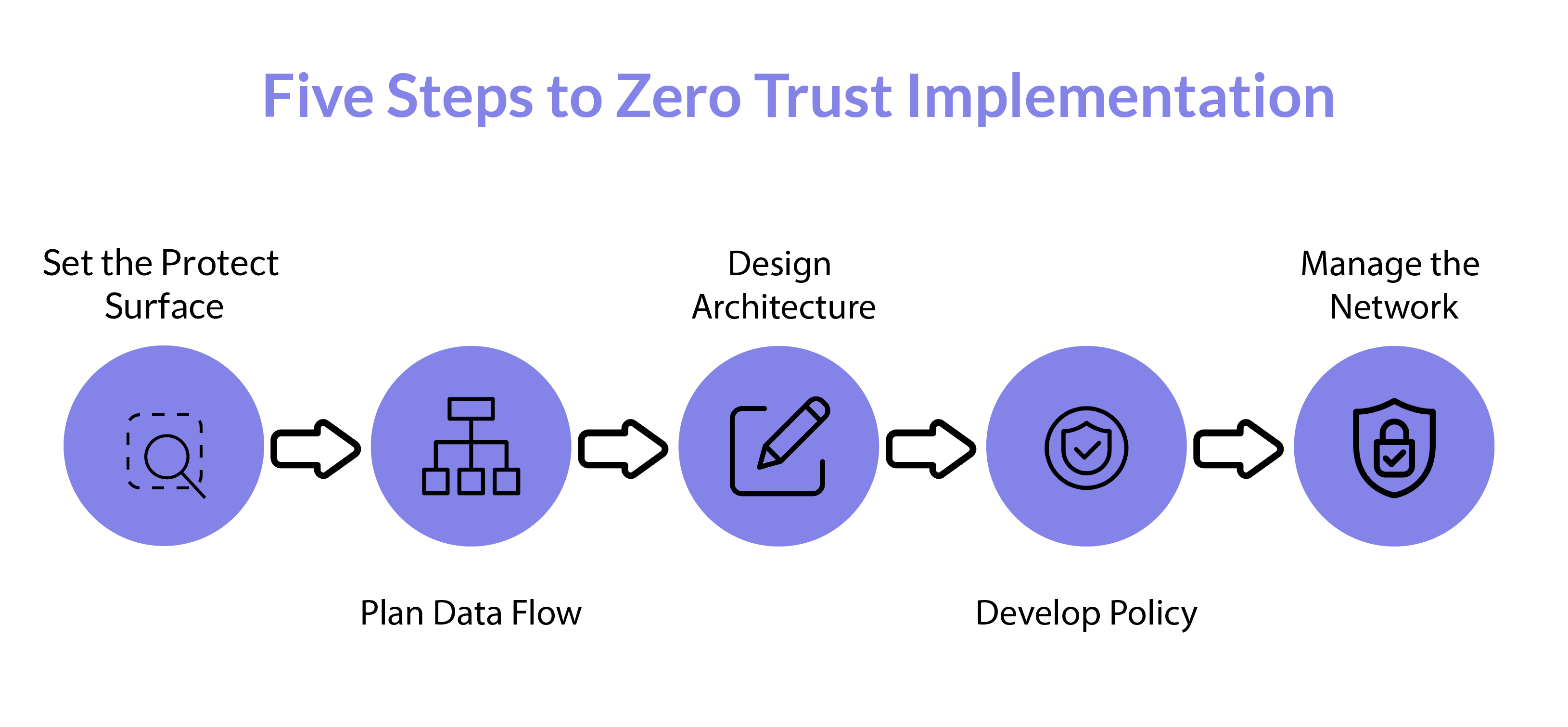
How To Implement Zero Trust Security Geniusee

Why You Need 6 Layers Of Zero Trust Control

Three Fundamentals To A Successful Zero Trust Rollout

Three Fundamentals To A Successful Zero Trust Rollout

R17 TAK PERLU TAKUT KEBOBOLAN LAGI AMANKAN DATA DENGAN SISTEM ZERO
Thank you for picking to discover our website. We all the best hope your experience surpasses your assumptions, which you uncover all the information and resources about Zero Trust Policy Example that you are looking for. Our dedication is to offer an user-friendly and interesting system, so feel free to browse with our web pages effortlessly.